
Travel as a Vulnerability, Not Just Movement
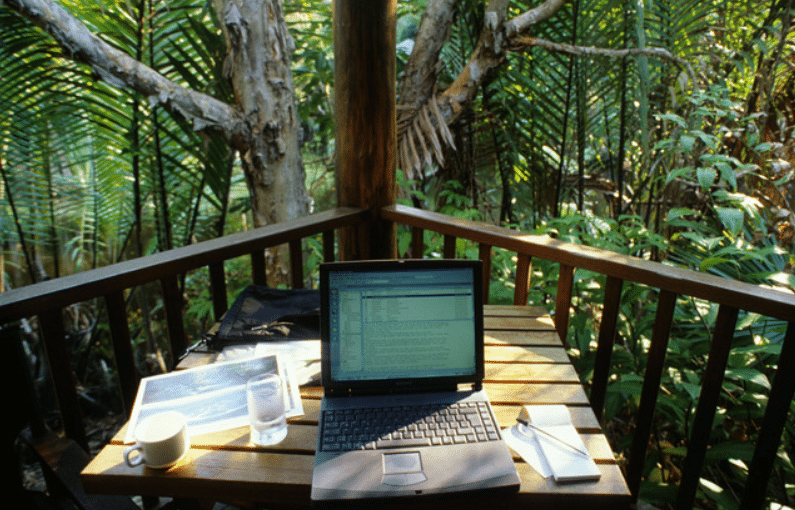
When personnel travel, they not only move physically—they also move data, access systems remotely, and interact with unfamiliar environments. This creates a combination of exposure points that are often underestimated.
In controlled office environments, networks are secured, devices are monitored, and access is regulated. During travel, these safeguards are reduced or removed entirely. Public networks, shared spaces, and temporary accommodations introduce variables that cannot be fully controlled.
The result is a shift from protected to exposed.
This exposure does not require sophisticated attacks. In many cases, simple oversight—connecting to an unsecured network, leaving a device unattended, or discussing sensitive information in public—can lead to compromise.
Understanding travel as a vulnerability is the first step in managing it.
Digital Threats: Networks, Devices, and Access
The most obvious risks during travel are digital. Devices such as laptops, tablets, and smartphones carry valuable data and provide access to corporate systems. If compromised, they can become entry points for wider breaches.
Public Wi-Fi networks are one of the most common threats. These networks are often unsecured, allowing data to be intercepted by anyone with the right tools. Even networks that appear legitimate can be spoofed, leading users to connect to malicious access points.
Device security becomes critical in this context. Strong authentication, encryption, and controlled access reduce the likelihood of compromise. However, technical measures alone are not sufficient. Behaviour plays a significant role.
Connecting only to trusted networks, avoiding unnecessary data access, and limiting the use of sensitive systems while travelling all contribute to reducing exposure.
Physical Security of Information
Information security is not limited to digital systems. Physical access to devices and documents presents an equally significant risk.
In hotels, airports, or vehicles, devices can be lost, stolen, or accessed without the owner’s knowledge. Even brief moments of inattention can create opportunities for compromise. A laptop left unattended in a meeting room or a phone placed on a table in a public area may be accessed in seconds.
This risk extends to physical documents as well. Printed materials, notes, and identification documents can reveal sensitive information if not handled properly.
Maintaining physical control of all devices and documents is essential. This requires discipline, not convenience. Secure storage, controlled access, and constant awareness reduce the likelihood of loss or unauthorised access.
Human Behaviour: The Most Overlooked Risk
The most significant vulnerabilities in information security are often behavioural. People tend to relax their standards while travelling, especially in informal environments. Conversations become more casual, devices are used more freely, and awareness decreases.
This creates opportunities for information leakage.
Sensitive discussions in public spaces, such as airports, hotels, or restaurants, can be overheard. Even if the information shared appears insignificant, it may provide context that can be exploited.
Social engineering is another concern. Individuals may attempt to gain information through conversation, presenting themselves as colleagues, service providers, or local contacts. Without verification, these interactions can lead to unintended disclosure.
Maintaining awareness of what is being shared, where it is being shared, and who is present is critical. Information security is not only about protecting systems, but also about controlling communication.
Data Minimisation: Carry Less, Risk Less
One of the most effective ways to reduce risk is to limit the amount of data carried during travel. The more information that is accessible, the greater the potential impact of a compromise.
Data minimisation involves preparing devices specifically for travel. This may include removing unnecessary files, limiting access to sensitive systems, and using temporary or restricted accounts. In some cases, dedicated travel devices are used to separate operational data from personal or corporate systems.
This approach ensures that even if a device is compromised, the impact is contained.
It also reinforces the principle that not all data needs to be available at all times.
Operational Awareness in Hostile Environments
In certain regions, information security risks extend beyond opportunistic threats. Hostile environments may include deliberate attempts to access or monitor data. This can involve surveillance, network interception, or targeted approaches to personnel.
In these contexts, awareness must be elevated.
Personnel must assume that communications may be monitored and that devices may be accessed. This does not mean avoiding all communication, but it does require adjusting behaviour accordingly. Sensitive discussions should be limited, and secure communication channels should be prioritised.
At N9BO℠, HEAT training addresses these realities by integrating information security into broader operational awareness. Personnel are trained to recognise not only physical threats, but also information-based risks.
Procedures and Consistency
Information security during travel is not achieved through isolated actions. It requires consistent application of procedures. These procedures must be clear, practical, and understood by all personnel.
This includes guidelines for:
- Device use and storage
- Network access
- Communication protocols
- Incident reporting
Consistency ensures that security is maintained even when conditions change. It reduces reliance on individual judgement and provides a framework for action.
Without procedures, security becomes dependent on memory and improvisation, both of which are unreliable under pressure.
Training: Turning Awareness into Behaviour
Awareness alone is not enough. Personnel may understand the risks but still fail to act appropriately if those risks are not reinforced through training.
Training bridges this gap. It provides practical scenarios, reinforces correct behaviour, and ensures that procedures are understood and applied consistently. This transforms information security from a concept into a habit.
At N9BO℠, training programmes emphasise the integration of information security into everyday operations. The objective is not to create specialists, but to ensure that all personnel operate with a baseline level of awareness and discipline.
Final Perspective
Travelling in high-risk environments introduces vulnerabilities that are often overlooked. Information, like personnel, becomes exposed when it moves outside controlled settings.
Protecting this information requires more than technical solutions. It requires awareness, discipline, and consistent behaviour. Devices must be secured, communication must be controlled, and data must be managed carefully.
In hostile environments, information can be as valuable as any physical asset.
Protecting it is not optional.
Secure Your Operations Beyond the Office
Contact N9BO℠ to integrate information security awareness into your HEAT training and protect your data in high-risk environments.









